I listed some of my favorite and useful Internet websites and network tools in previous post which has been used in my daily IT life. There are some network security related tools I am using at my environment. This post is a summarize for those tools and also I am trying to extend this list to add more later.
Table of Contents
Online Security Scanning
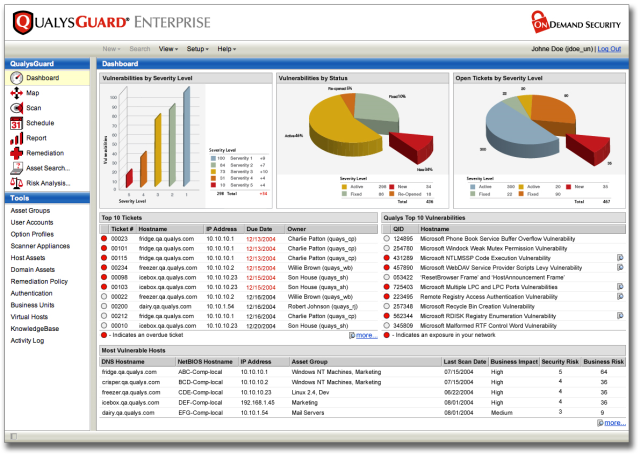
- Qualys FreeScan – Online Vulnerability Scan can accurately scan your network, servers, desktops or web apps for security vulnerabilities. Scanning takes just minutes to find out where you’re at risk.
- Zscaler – Free, Instant Security Scan is a comprehensive suite of security services delivered from the cloud. It covers email, web and mobile computing. Some services the product provides are anti-malware, browser and application vulnerability management, policy enforcement for mobile computing, bandwidth and QoS management, web filtering, intellectual property protection and regulatory compliance.
- Acunetix analyze complete web and network from Acunetix servers. You can register for free but full function 14 days online scan. 46% of web applications scanned with Acunetix Online Vulnerability Scanner contained a high risk vulnerability and 87% a medium risk vulnerability as per the 2015 Web App Vulnerability Report by Acunetix
- Scan my server: provide one of the most comprehensive reports of varieties of security test like SQL Injection, Cross Site Scripting, PHP Code Injection, Source Disclosure, HTTP Header Injection, Blind SQL Injection and much more. Scan report is notified by email with vulnerability summary. But it requires you put a verification seal on your website to confirm your site ownership.
Online Website Security Vulnerabilities & Malware Scan
- ASafaWeb – Automated Security Analyser for ASP.NET Websites. You also can schedule a regular scanning for your website in case there is any security level change on your website and you will be notified at the first tim.
- Qualus SSL Labs: provides deep analysis of your https URL including expiry day, overall rating, Cipher, SSL/TLS version, Handshake simulation, Protocol details, BEAST and much more.
- Quttera – Free Online Website Malware Scanner checks website for malware and vulnerability exploits online
- SiteGuarding: helps you to scan your domain for malware, website blacklisting, injected spam, defacement and much more. The scanner is compatible with WordPress, Joomla, Drupal, Magento, osCommerce, Bulletin and another platform.
- Sucuri – Free Website Malware and Security Scanner
- Tinfoil Security : first audits your website against top 10 OWASP vulnerabilities and then other known security holes. You will need to verify your site by upload a html file, or add a meta tag, or add a DNS record, or manual Tinfoil verification.
- UpGuard : is external risk assessment tool uses publicly available information to grade on various factors including SSL, Clickjack attack, Cookie, DNSSEC, Headers, etc.
- VirusTotal is a free service that analyzes suspicious files and URLs and facilitates the quick detection of viruses, worms, trojans, and all kinds of malware.
- Web Inspector – Scan a Webpage with entering a URL to find out whether it is malicious or not
Free Security Check / Scanning Tools
- Microsoft Baseline Security Analyzer (MBSA) can perform local or remote scans on Windows desktops and servers, identifying any missing service packs, security patches, and common security misconfigurations.
- Tripwire Free Tools : SecureScan and SecureCheq – SecureScan finds security vulnerabilities on your network with Tripwire SecureScan and get instructions on how to fix them. Tripwire SecureCheq is free Microsoft Windows Configuration Security Check tool for Desktops and Servers. It tests for common configuration errors and weaknesses in Microsoft Windows desktops and servers.
- Retina Gives You Powerful Vulnerability Assessment Across Your Entire Environment. For up to 256 IPs free, Retina Community identifies network vulnerabilities (including zero-day), configuration issues, and missing patches across operating systems, applications, devices, and virtual environments.
- OpenVAS is a framework of several services and tools offering a comprehensive and powerful vulnerability scanning and vulnerability management solution.
Packets Capturing and Analysing Tools
- Tcpdump – Packet sniffers
- Wireshark – Wireshark (known as Ethereal until a trademark dispute in Summer 2006) is a fantastic open source multi-platform network protocol analyzer. It allows you to examine data from a live network or from a capture file on disk. You can interactively browse the capture data, delving down into just the level of packet detail you need. Wireshark has several powerful features, including a rich display filter language and the ability to view the reconstructed stream of a TCP session. It also supports hundreds of protocols and media types. A tcpdump-like console version named tshark is included. One word of caution is that Wireshark has suffered from dozens of remotely exploitable security holes, so stay up-to-date and be wary of running it on untrusted or hostile networks (such as security conferences).
- CloudShark works entirely in your web browser. No additional utilities, plugins, or downloads.
TCP/UDP Tools
- TCPView is a Windows program that will show you detailed listings of all TCP and UDP endpoints on your system, including the local and remote addresses and state of TCP connections.
- The Process Explorer display details your computer’s running processes in a more visual representation than the standard Windows Task Manager.
- RINETD – Redirects TCP connections from one IP address and port to another.
Integrity Check
- Tripwire – It was a simple tool to check file and folder integrity. Now Tripwire provide a whole set solution to discovers every asset on an organization’s network and delivers high-fidelity visibility and deep intelligence about these endpoints. Tripwire solutions also deliver actionable reports and alerts and enable the integration of valuable endpoint intelligence into operational systems like change management databases, ticketing systems, patch management and security solutions including SIEMS, malware detection and risk and analytics.
Penetration Test Tools
- World’s most used penetration testing software – metasploit
- Kali Linux – is the new generation of the industry-leading Debian-based BackTrack Linux penetration testing and security auditing Linux distribution. Kali Linux is a complete re-build of BackTrack from the ground up, adhering completely to Debian development standards. Kali 2.0 Teaser is coming.
- Nessus® is the industry’s most widely-deployed vulnerability, configuration, and compliance scanner.
- BackTrack – BackTrack is a free bootable Linux distribution that contains a plethora of open source tools that you can use for network security and penetration testing. The tools are organized into different categories such as ‘Information Gathering’, ‘Vulnerability Assessment’, ‘Exploitation Tools’, ‘Privilege Escalation’ and ‘Maintaining Access’, amongst others.
- Nmap (“Network Mapper”) is a free and open source (license) utility for network discovery and security auditing.
Proxy Software
Network Automation Tools
- NetMRI provides automatic network discovery, switch port management, network change automation, and continuous security policy and configuration compliance management for multi-vendor routers, switches, and other layer-2 and layer-3 network devices. NetMRI is the only platform that supports traditional and virtual network constructs (such as VRF) for multi-vendor network automation.
Security Intelligence Tools
- Lancope, Inc. is a leading provider of network visibility and security intelligence to protect enterprises against today’s top threats.
- FireEye Network Security (NX) products, now available in modular 2- and 4-Gbps appliances, enable organizations to prevent, detect, and respond to network-based zero day exploit attempts, web drive-by downloads, and advanced malware that routinely bypass conventional signature-reliant defenses.
Security information and event management (SIEM)
- IBM® Security QRadar® SIEM consolidates log source event data from thousands of devices endpoints and applications distributed throughout a network.
- Splunk is an industry-leading platform for machine data, automatically indexes all your log data, including structured, unstructured and complex multi-line application log data.
Encryption Tools
- Truecrypt – a strong encryption utility that can encrypt entire volumes or create an encrypted container within a file system. It has been announced this freeware project no longer maintained on 28 May 2014.
Windows System/Appication Test Software
- Sandboxie, which lets you run programs independent of the rest of your system. That way they can’t infect, access, or otherwise interfere with your Windows installation. It supports 64bits and Win8.
- PowerShadow works both pro-actively and protectively to shield you from anything that threatens the life of your computer system. Installation of PowerShadow is like planting an amazing protection mechanism called the Shadow Mode. It is designed to defend you against millions of viruses, spyware and Trojan horse that would love to invade your system.
Antivirus
- Avast! Free Antivirus. The testing result from third party is pretty good.
Firewall Management Tools
- Tufin Orchestration Suite: Tufin enables organizations to implement network security changes in the same business day through automation and impact analysis – orchestrating change processes end-to-end across physical environments and hybrid cloud platforms. It automatically designs, provisions, analyzes and audits network changes from the application layer down to the network layer.

- FireMon provides enterprises with security management software that gives them deeper visibility and tighter control over their network security infrastructure. Its Security Intelligence Platform–including Security Manager, Policy Planner, Policy Optimizer and Risk Analyzer–enables customers to identify network risk, proactively eliminate those vulnerabilities and strengthen security throughout the organization, and reduce the cost of security operations.
- The AlgoSec Security Management Suite: The AlgoSec suite delivers a complete, integrated software solution for managing complex network security policies — from the business application layer to the network infrastructure. With powerful visibility across virtual, cloud and physical environments, the AlgoSec suite automates and simplifies the entire security change management process to accelerate application delivery while ensuring security and compliance. The AlgoSec Security Management Suite, which includes Algosec BusinessFlow®, AlgoSec FireFlow® and AlgoSec Firewall Analyzer helps you.

