This is the third part of Checkpoint SSL VPN Series LAB.
Part 1: Enable Checkpoint SSL VPN Remote Access: Step by Step Instruction Part 1 (Local User Authentication)
Part 2: Enable Checkpoint SSL VPN Remote Access: Step by Step Instruction Part 2 (AD Authentication)
Part 3: Enable Checkpoint SSL VPN Remote Access: Step by Step Instruction Part 3 (Certs and Two Factor Authentication)
Part 4: Enable Checkpoint SSL VPN Remote Access: Step by Step Part 4 – Two Factor Authentication (AD and SMS)
In this part, it will introduce how to use Checkpoint Internal CA issued Certs and how to enable two factor authentication using certs and AD accounts.
In Part 2, AD authentication has been tested and next step is to create certificate for each remote user.
Table of Contents
Enable Certificate Authentication Steps:
1. Create Certificate for user test2.
2. Click OK after enter all information for Certificate File.
3. Once certificate created, it will show in the list. It also can be revoked.
4. Import Certificate into Client Machine
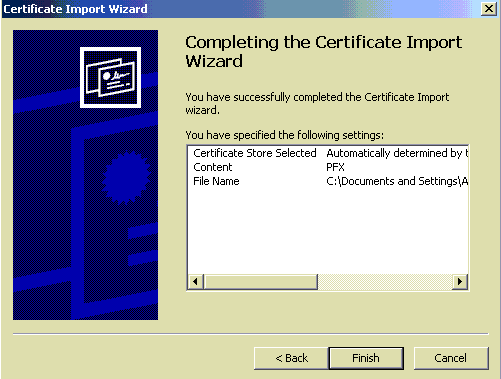
Double click the cert file from Client Machine. It will enable Certificate Import Wizard. Enter your password, click next and next then it will be completed this import.
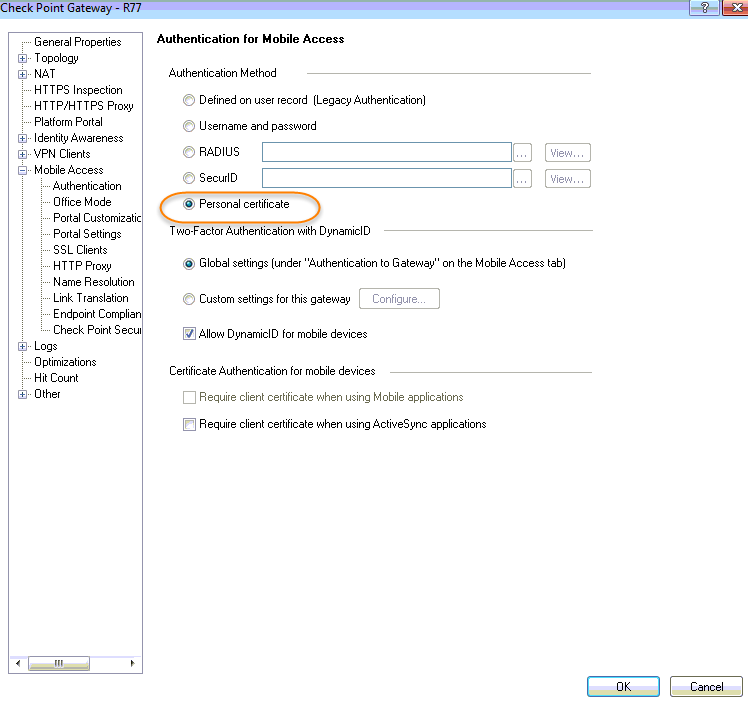
5. Change authentication method to from Username and Password to Personal Certificate on the Gateway Properties:
6. After installed polices to gateway, test it from Client Machine with your imported Personal Certificate:
Enable two factor authentication (Certs and AD account) Steps
1. Certificate will be the first method and AD username/password will be second factor.
Here is the list Supported Authentication Schemes Combinations:
2. GuiDBedit Tool
It will be used to configure Multiple Authentication Schemes to allow the administrator to request multiple proofs of user’s identity. In our case, for example, request the user to install his certificate and enter his AD password for authenticating.
GuiDBedit Tool will be found at C:Program Files (x86)CheckPointSmartConsoleRXXPROGRAMGuiDBedit.exe
3. Verify the first factor authentication is Certificates.
It will be found at Tables -> Network Objects ->network_objects.
Found the Gateway / Cluster object, in this case , for example, it is R77.
From lower pane, check the value of realms_for blades-> ssl_vpn ->authentication-> auth_schemes->Element Index 0 -> auth_scheme.
It is certificate which is configured before thorough Smart Dashboard.
4. right click on ‘auth_schemes’ ,-> ‘Add…’
5. Enter a value for Index:
1 for the second authentication scheme. 0 is already there for 1st factor, which is ‘Element Index 0’
6. Go to ‘Element Index 1’, right click on ‘auth_scheme’ -> ‘Edit…’. Choose ‘user_pass’ for AD username and password as 2nd factor.
7. Save the changes (‘File’ menu – ‘Save All’).
Close the GuiDBedit Tool. Connect to Security Management Server with SmartDashboard. Install the policy onto Security Gateway / Cluster object.
8. Test
Reference:
1. Multiple Authentication Schemes for Mobile Access